In the previous article, we stopped at...
Read More
Cyber Sharing
Don’t worry when someone tells you that you’re wasting time reading books or articles on tech-sharing platforms. Everything you read gives you some knowledge — maybe not much, but one day, that small piece of understanding will make a difference.
Exploit #03: Web Shell
With the rapid development of technology today,...
Read MoreR&E #04: Service Enumeration
In today’s article, we’ll move on to...
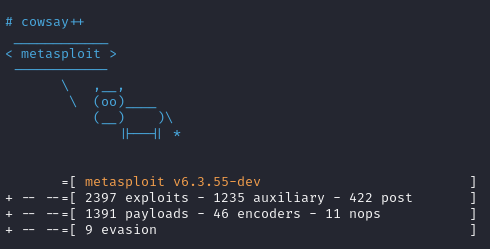
Read MoreExploit #02: Meterpreter
Today we’ll come back to the topic...
Read MoreUsing cURL for basic web…..exploitation
Applications like the browsers we use every...
Read MoreR&E #03: Gathering System Information (Host Enumeration)
Today’s post will be about host enumeration....
Read MoreLinux 101 #03: Linux Workflow (Cont)
A file descriptor (FD) in Unix/Linux operating...
Read MoreLinux 101 #02: Linux Workflow
Let us start with the navigation. Before...
Read MoreLinux 101 #01: Meet Linux: What It Is, Where It Came From, and How It’s Built
Linux, as you might already know, is...
Read More