With the rapid development of technology today, it’s almost guaranteed...
Read More
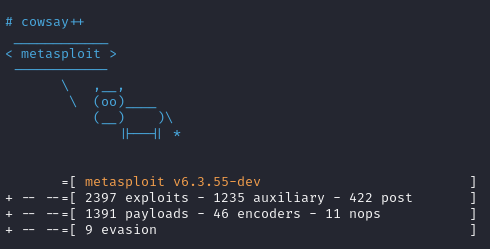
Exploitation
Exploitation — this is the phase most people find the most exciting. It’s when you begin actively attacking the target and look for a reliable foothold to establish access in the target network. Take your time here: a well-chosen entry point matters more than a rushed attempt.
Exploit #02: Meterpreter
Today we’ll come back to the topic of shells. In...
Read MoreExploit #01: Types of Shells – Not just bash shell
Once we compromise a system and exploit a vulnerability to...
Read More