THM [Easy Lab] - TakeOver
This challenge revolves around subdomain enumeration.
Okay, first of all, the challenge already tells us that they have a domain named https://futurevera.thm.
As the room title suggests, this room only requires subdomain enumeration and does not need much exploitation. Therefore, we will focus on discovering the hidden subdomains in this challenge.
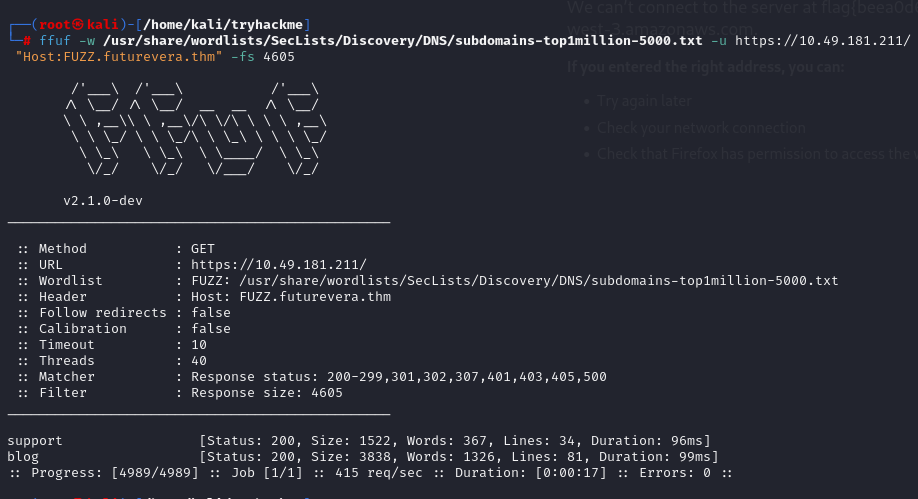
Add the domain above to the hosts file on my attacking machine, then I use ffuf to enumerate subdomains, which returns two subdomains: blog and support. Now let’s try accessing these two subdomains to see if there is anything interesting.
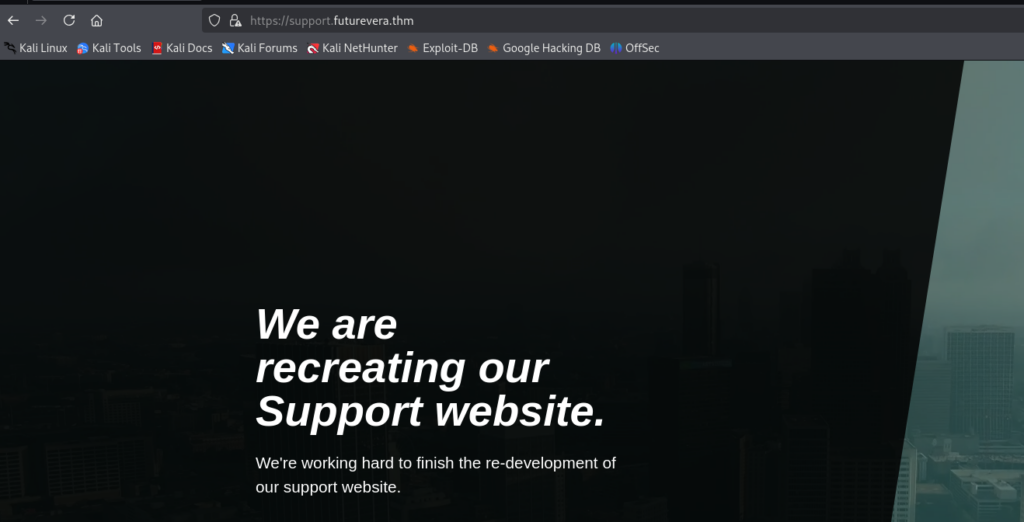
When accessing the blog subdomain, I get a server not found error, but when I access the support subdomain, it redirects me to a new web page.
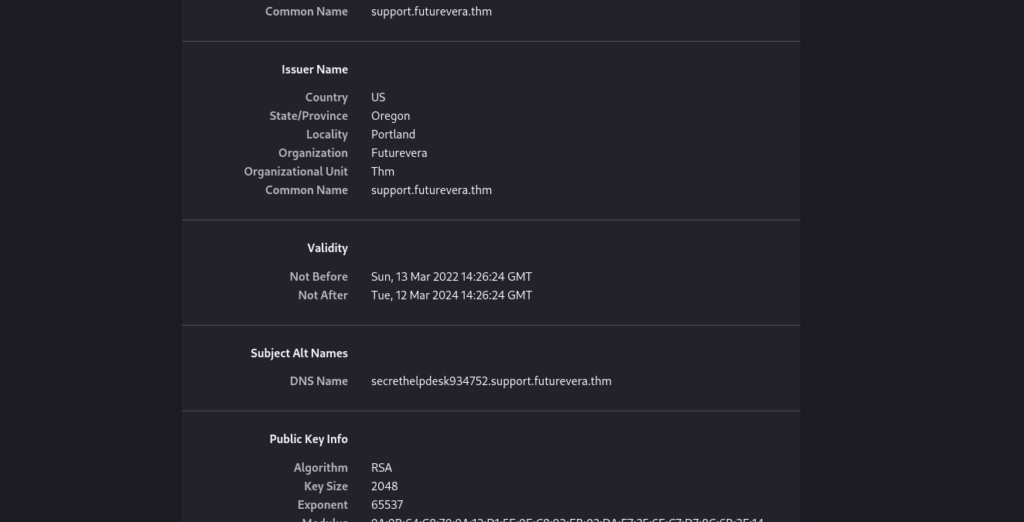
I tried checking the page source, but there wasn’t anything particularly useful. Then I checked the SSL certificate and discovered a third subdomain.
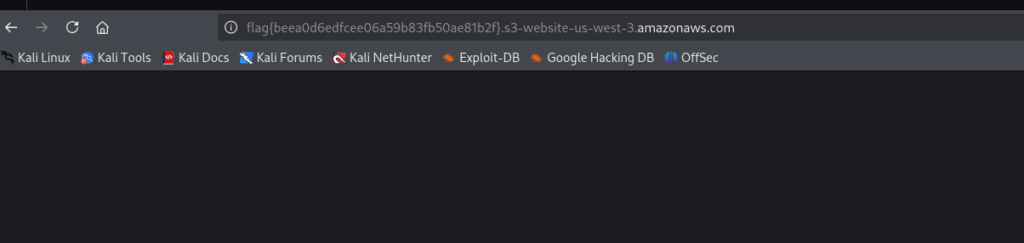
At this point, I accessed this subdomain. When accessing it via HTTPS, it redirected me back to the same web page as the main domain futurevera.thm. I continued checking the source code and other things, but nothing looked promising, until I tried using HTTP instead of HTTPS. Before running ffuf, I had already scanned the IP with Nmap and saw that ports 80 and 443 were open. And then boom — it redirected me to a new URL, which turned out to be the flag for this room.
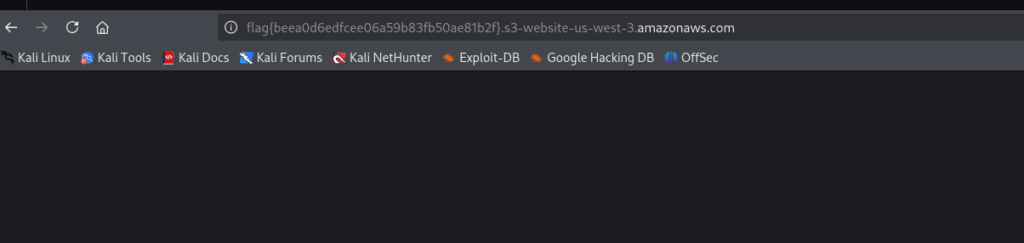
At this point, I accessed this subdomain. When accessing it via HTTPS, it redirected me back to the same web page as the main domain futurevera.thm. I continued checking the source code and other things, but nothing looked promising, until I tried using HTTP instead of HTTPS. Before running ffuf, I had already scanned the IP with Nmap and saw that ports 80 and 443 were open. And then boom — it redirected me to a new URL, which turned out to be the flag for this room.
Note: When you discover new subdomains, you need to add them to the hosts file on your attack machine.
Read more to learn something new with this room.